Thursday 01 January 2026 (1 post)
La liste rituelle, qui s'est un peu élargie cette année:
- Emilia Pérez: 15 janvier 2025, MK2 Bibliothèque
- Babygirl: 16 janvier 2025, MK2 Bibliothèque
- 5 septembre: 11 février 2025, MK2 Bibliothèque
- Mickey 17: 9 mars 2025, MK2 Quai de Loire
- The insider: 9 avril 2025 MK2 Bibliothèque
- Pink Floyd - Live at Pompeii: 28 avril 2025, Pathé Rennes
- Les règles de l’art: 6 mai 2025, MK2 Quai de Seine
- Thunderbolts*: 7 mai 2025, UGC Montparnasse
- La venue de l’avenir: 25 mai 2025, MK2 Bastille
- Fils de.: 22 septembre 2025, MK2 Quai de Loire
- Sirat: 4 novembre 2025, MK2 Quai de Seine
- Zootopia 2: 6 décembre 2025, Pathé Rennes
- Bugonia: 10 décembre 2025, MK2 Quai de Loire
Une bonne année j'ai trouvé.
Corsac@15:20:59 (Echoes)
Sunday 21 December 2025 (1 post)
Aujourd'hui les jours rallongent \o/
Corsac@11:49:48 (Roadbook)
Wednesday 28 May 2025 (1 post)
As a small addendum to the last post, here are the relevant
commands #debci helpfully provided.
First, you need to install the autopkgtest package,
obviously:
# apt install autopkgtest
Then you need to create a Debian virtual machine to run the
tests (put the sid.raw wherever you prefer):
# autopkgtest-build-qemu sid /tmp/sid.raw
Then you can run the tests themselves, using the just created
virtual machine. The autopkgtest command can use the tests from
various sources, using the last argument to the command. In my case
what was the most helpful was to run the tests from my git clone
(which uses gbp) so I could edit the tests directly. So I didn't
give anything for testsrc (but
. would work as well I guess).
$ autopkgtest -BU --add-apt-release=unstable
--pin-packages=unstable=strongswan -- qemu /tmp/sid.raw
--ram-size=4096 --cpus=1
Then I could play with the tests themselves, the number of CPU
for the Qemu VM, and run everything in a loop.
Yves-Alexis@13:12:16 (Debian)
Friday 23 May 2025 (1 post)
For a while, the strongSwan Debian package had an autopktest.
The initial version was proposed by Christian Ehrhardt in 2016
(presumably especially for downstream use in Ubuntu) and updated in
2019, but since then not much at least in Debian.
With the metapackage dependencies update in 6.0.0-1 I had to
tune a bit the tests dependencies so they wouldn't totally fail,
and I noticed the amd64 tests were failing since basically the
beginning (the other architectures would pass, but because the
tests wouldn't actually run at all since they rely on the
isolation-machine restriction which is
not available there.
So I tried to fix them, and it actually took me quite a while
because I wasn't able to run the tests locally easily and the salsa
CI doesn't have the isolation-machine
restriction either. And some tests would pass and not
other.
With some nice help from #debci, and using my newly received X13G5 I set
up an autopkgtest VM and started experimenting. The 6.0.0-4
autopkgtests were failing 19 times over 20 steps, but passing one
time. So it looked like a race condition, which we narrowed to the
fact that starting the daemons (using invoke-rc.d which calls systemctl) is asynchronous. So depending on the load
and maybe the machine, the tests would usually fail but sometime
pass.
There's no easy way to make the call synchronous, so as a
stopgap I added a small sleep 1 command and it fixed it for now.
Tada! strongSwan has now passing
autopkgtests in unstable (and testing) amd64. It's not entirely
satisfying but still.
Next steps would be to add tests for the new daemon using the
swanctl inteface, but that'll be for Forky (Trixie+1).
Yves-Alexis@14:49:26 (Debian)
Thursday 15 May 2025 (1 post)
After more than ten years on my trusted X250, and with a lot of financial help for Debian (which I really thank, more on that later), I finally jumped on a new ThinkPad, an X13 Gen 5.
The migration path was really easy: I'm doing daily backups with borg of the whole filesystems on an encrypted USB drive, so I just had to boot a live USB key on the new laptop, plug the USB drive, create the partitioning (encryption, LVM etc.) and then run borg extract. Since I'm using LABEL in the various fstab I didn't have much to change.
I actually had a small hiccup because my daily backup scripts used ProtectKernelModules and besides preventing loading modules into the running kernel, it also prevents access to /usr/lib/modules. So when restoring I didn't have any modules for the installed kernels. No big deal, I reinstalled the kernel package from the chroot and it did work just fine.
All in all it was pretty smooth.
I've started a similar page as the X250 for the X13G5 but honestly I don't think I'll have to document a lot of stuff because everything basically works out of the box. It's not really a surprise because we went a long way since 2015 and Linux kernels are really tested on a lot of hardware, including laptops these days, and Intel laptops are the most standard stuff you can find. I guess it's still rocky for ARM64 laptops (and especially Apple hardware) but the point was less to do porting work for Debian and rather beeing more efficient for the current stuff I maintain (and sometimes struggle with).
As said above, the laptop has been funded by Debian and I really thank the DPL and the Debian France treasurer for authorizing it and beeing really fast on the reimbursement.
I had already posted a long time ago about hardware funding for Debian developers. It took me quite a while but I finally managed to ask for help because I couldn't afford the hardware at this point and it was becoming problematic. This is not something which should be done lightly (Debian wouldn't have the funds) but this is definitely something which should be done if needed. Don't hesitate to ask your fellow Debian developpers about advice on this.
Yves-Alexis@20:19:43 (Debian)
Saturday 04 January 2025 (1 post)
Le rituel de la nouvelle année, les films de l'année précédente.
- Dune Part Two: 10 mars 024, UGC Ciné Cité Bercy
- Le deuxième acte: 20 mai 2024, UGC Ciné Cité Bercy
- The Fall Guy: 21 mai 2024, UGC Ciné Cité Bercy
- Vice Versa 2: 4 août 2024, CGR Torcy
- Riverboom: 27 septembre 2024, MK2 Quai de Seine
- All we imagine as light: 8 octobre 2024, MK2 Quai de Seine
- Vaiana 2: 30 novembre 2024, MK2 Quai de Loire
- L’amour ouf: 1er décembre 2024, MK2 Quai de Seine
- Anora: 2 décembre 2024, MK2 Quai de Seine
- Jury n°2: 3 décembre 2024, MK2 Bibliothèque
- La plus précieuse des marchandises: 21 décembre 2024, Arvor
Une plutôt bonne année je dois dire, avec pas mal d'occasions et plutôt de chouettes films
Corsac@20:53:47 (Roadbook)
Saturday 21 December 2024 (1 post)
Aujourd'hui les jours rallongent \o/
Corsac@19:18:06 (Roadbook)
Monday 22 January 2024 (1 post)
J'ai enfin pris le temps de nettoyer un peu ma chaîne de vélo
et de la graisser, et ça change la vie. C'était extrêmement
agréable ce matin (plus de bruit et plus de « saut » de dent sur
le petit pignon).
Corsac@13:28:13 (Roadbook)
Sunday 07 January 2024 (1 post)
- Avatar: la voix de l’eau: 7 janvier 2023, MK2 Quai de Loire
- Babylon: 24 janvier 2023, MK2 Bibliothèque
- Asterix et Obelix: l’empire du milieu: 22 février 2023, MK2 Quai de Loire
- Mission: impossible Dead reckoning (part 1): 25 juillet 2023, MK2 Bibliothèque
- Oppenheimer: 18 août 2023, UGC Ciné Cité Bercy
- Le livre des solutions: 12 septembre 2023, MK2 Quai de Seine
- Anatomie d’une chute: 26 septembre 2023, MK2 Quai de Seine
- Le théorème de Marguerite : 7 novembre 2023, MK2 Bibliothèque
Au rythme des allers-retours à Paris, comme qui dirait.
Corsac@23:43:39 (Echoes)
Friday 22 December 2023 (1 post)
Aujourd'hui les jours rallongent \o/
Corsac@03:27:19 (Roadbook)
Monday 02 January 2023 (1 post)
Ça faisait une paye que je n'étais pas plié à l'exercice,
d'autant que je ne vais quand même plus beaucoup au cinéma.
Pour la récolte 2022:
- La Ruse: 4 mai 2022, MK2 Bibliothèque
- Top Gun Maverick: 22 juin 2022, MK2 Quai de Loire
- Armageddon Time: 13 novembre 2022, MK2 Quai de Loire
- Wakanda Forever: 30 novembre 2022, MK2 Bibliothèque
Pas vraiment de quoi rentabiliser une carte illimitée (même au
prix actuel du billet) mais on va dire que c'est pour soutenir le
cinéma !
Corsac@09:33:54 (Roadbook)
Wednesday 21 December 2022 (1 post)
Aujourd'hui les jours rallongent \o/
Corsac@15:41:30 (Roadbook)
Tuesday 21 December 2021 (1 post)
Aujourd'hui les jours rallongent \o/
Corsac@14:56:53 (Roadbook)
Monday 21 December 2020 (1 post)
Aujourd'hui les jours rallongent \o/
Corsac@09:14:20 (Roadbook)
Saturday 19 December 2020 (1 post)
As a followup to the previous post, here's an update on the iOS
14 USB tethering problem on Linux. After some investigation, Matti
Vuorela
found that reducing the USB packet size by two bytes would
actually fix the issue. A small patch was later
commited to the Linux kernel and found its way to Linux and
distributions stable releases. On Debian stable you'll need to
upgrade to Buster 10.7 to get the
fix.
Yves-Alexis@11:14:08 (Debian)
Friday 16 October 2020 (1 post)
It's a bit of a long shot, but maybe someone on Planet Debian or
elsewhere can help us reach the right people at Apple.
Starting with iOS 14, something apparently changed on the way
USB tethering (also called Personal Hotspot) is set up, which broke
it for people using Linux. The driver in use is ipheth, developped
in 2009 and
included in the Linux kernel in
2010.
The kernel driver negotiates over USB with the iOS device in
order to setup the link. The protocol used by both parties to
communicate don't really seemed documented publicly, and it seems
the protocol has evolved over time and iOS versions, and the Linux
driver hasn't been kept up to date. On macOS and Windows the driver
apparently comes with iTunes, and Apple engineers obviously know
how to communicate with iOS devices, so iOS 14 is supported just
fine.
There's an open
bug on libimobildevice (the set of userlands tools used to
communicate with iOS devices, although the update should be done in
the
kernel), with some debugging and communication logs between
Windows and an iOS device, but so far no real progress has been
done. The link is enabled, the host gets an IP from the device, can
ping the device IP and can even resolve name using the device DNS
resolver, but IP forwarding seems disabled, no packet goes farther
than the device itself.
That means a lot of people upgrading to iOS 14 will suddenly
lose USB tethering. While Wi-Fi and Bluetooth connection sharing
still works, it's still suboptimal, so it'd be nice to fix the
kernel driver and support the latest protocol used in iOS 14.
If someone knows the right contact (or the right way to contact
them) at Apple so we can have access to some kind of documentation
on the protocol and the state machine to use, please reach us
(either to the libimobile device bug or to my email address
below).
Thanks!
Yves-Alexis@14:36:41 (Debian)
Friday 09 October 2020 (2 posts)
So, a bit more thank 18 months ago, I started a new adventure.
After a few flights with a friend of mine in a Robin DR400 and
Jodel aircrafts, I enlisted in a local flight club at the Lognes
airfield (LFPL), and started a Pilot Private License training. A
PPL is an international flight license for non commercial
operations. Associated with a qualification like the SEP (Single
Engine Piston), it enables you to fly basically anywhere in the
world (or at least anywhere where French is spoken by the air
traffic controllers) with passengers, under Visual Flight Rules
(VFR).


A bit like with cars, training has two parts, theoretical and
practical, both validated in a test. You don't have to pass the
theoretical test before starting the practical training, and it's
actually recommended to do both in parallel, especially since
nowadays most of the theoretical training is done online (you still
have to do 10h of in-person courses before taking the test).
So in March 2019 I started both trainings. Theoretical training is
divided in various domains, like regulations, flight mechanics,
meteorology, human factors etc. and you can obviously train in
parallel. Practical is more sequential and starts with basic flight
training (turns, climbs, descents), then take-off, then landing
configuration, then landing itself. All of that obviously with a
flight instructor sitting next to you (you're on the left seat but
the FI is the “pilot in command”). You then start doing circuit
patterns, meaning you take off, do a circuit around the airfield,
then land on the runway you just took off. Usually you actually
don't do a complete landing but rather touch and go, and do it
again in order to have more and more landing training.
Once you know how to take-off, do a pattern and land when
everything is OK, you start practicing (still with your flight
instructor aboard) various failures: especially engine failures at
take off, but also flaps failure and stuff like that, all that
while still doing patterns and practicing landings. At one point,
the flight instructor deems you ready: he exits the plane, and you
start your first solo flight: engine tests, take off, one pattern,
landing.
For me practical training was done in an Aquila AT-01/A210, which
is a small 2-seater. It's really light (it can actually be used as
an ultralight), empty weight is a bit above 500kg and max weight is
750. It doesn't go really fast (it cruises at around 100 knots, 185
km/h) but it's nice to fly. As it's really lightweight the wind
really shakes it though and it can be a bit hard to land because it
really glides very well (with a lift-to-drag ratio at 14). I tried
to fly a lot in the beginning, so the basic flight training was
done in about 6 months and 23 flight hours. At that point my
instructor stepped out of the plane and I did my first solo flight.
Everything actually went just fine, because we did repeat a lot
before that, so it wasn't even that scary. I guess I will remember
my whole life, as people said, but it was pretty uneventful,
although the controller did scold me a little because when taxiing
back to the parking I misunderstood the instructions and didn't
stop where asked (no runway incursion though).



After the first solo flight, you keep practicing patterns and solo
flights every once in a while, and start doing cross-country
flights: you're not restricted to the local airfields (LFPL, LFAI,
LFPK) but start planning trips to more remote airports, about 30-40
minutes away (for me it was Moret/LFPU, Troyes/LFQB,
Pontoise/LFPT). Cross country flights requires you to plan the
route (draw it on the map, and write a navigation log so you know
what to do when in flight), but also check the weather, relevant
information, especially NOTAMs - Notice To Air Men (I hope someone
rename those Notice to Air Crews at one point), estimate the fuel
needed etc. For me, flight preparation time was between once and
twice the flight time. Early flight preparation is completed on the
day by last-minute checks, especially for weather. During the
briefing (with the flight instructor at first, but for the test
with the flight examiner and later with yourself) you check in turn
every bit of information to decide if you're GO or not for the
flight. As a lot of things in aviation, safety is really paramount
here.


Once you've practiced cross country flight a bit, you start
learning what to do in case of failures during a non-local flights,
for example an engine failure in a middle of nowhere, when you have
to chose a proper field to land, or a radio failure. And again when
you're ready for it (and in case of my local club, once you pass
your theoretical exam) you go for cross-country solo flights (of
the 10h of solo flight required for taking the test, 5h should be
done in cross-country flights). I went again to Troyes (LFQB), then
Dijon-Darois (LFGI) and did a three-legs flight to Chalons-Ecury
(LFQK) and Pont sur Yonne (LFGO).
And just after that, when I was starting to feel ready for the
test, COVID-19 lockdown happened, grounding everyone for a few
months. Even after it was over, I felt a bit rusty and had to take
some more training. I finally took the test in the beginning of
summer, but the first attempt wasn't good enough: I was really
stressed, and maybe not completely ready actually. So a bit more
training during summer, and finally in September I took the final
test part, which was successful this time.
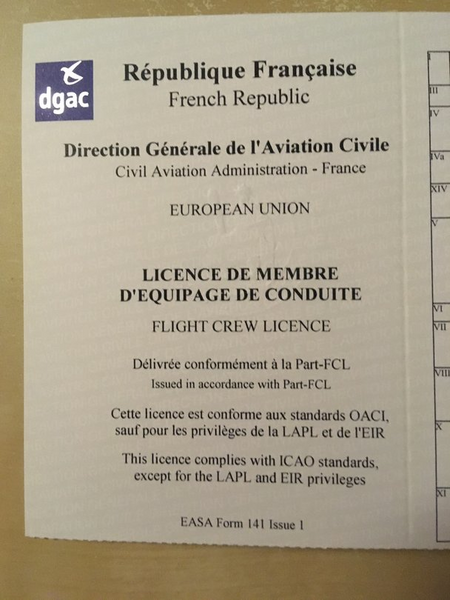
After some paperwork, a new, shiny, Pilot Private License arrived
at my door.
And now that I can fly basically when I want, the autumn is finally
here with bad weather all day long, so actually planning real
flights is a bit tricky. For now I'm still flying solo on familiar
trips, but at some point I should be able to bring a passenger with
me (on the Aquila) and at some point migrate to a four-seaters like
the DR400, ubiquitous in France.



Yves-Alexis@18:37:21 (Debian)
Il y a un peu plus de 18 mois, je me suis embarqué dans une nouvelle aventure. Après quelques vols avec un ami en DR400 et en Jodel, je me suis inscris dans un aéro-club à l'aérodrome de Lognes (LFPL) et j'ai débuté une formation de pilote privé. Le PPL est une licence reconnue internationalement qui permet de faire des vols non commerciaux. Elle est associé à une qualification de classe d'avions (comme SEP pour les avions monomoteur à piston) et permet de voler n'importe où dans le monde (ou disons pour l'instant n'importe où où le français est une langue officielle parlée par les contrôleurs aériens) avec des passagers, selon les règles du vol à vue.


Un peu comme le permis voiture, la formation comporte deux parties, théorique et pratique, avec un examen pour chacune. On peut commencer la formation pratique avant d'avoir la partie théorique (avant même de commencer d'ailleurs), et c'est même recommandé de faire les deux en parallèle, d'autant plus que de nos jours la majeure partie de la formation théorique est faite en ligne (il y a tout de même 10h de cours physiques).
En mars 2019, j'ai donc commencé les deux parties. La partie théorique couvre différents domaines: règlementation, mécanique du vol, météo, facteurs humains etc. et il est évidemment possible d'avancer en parallèle. La partie pratique est plutôt séquentielle et démarre par des exercices de maniabilité (virages, montées, descentes), puis les décollages, l'approche de l'atterrissage, puis l'atterrissage lui-même. Tout ça évidemment avec un instructeur assis à côté (l'élève est en place gauche mais c'est bien l'instructeur qui est commandant de bord, même si au fur et à mesure des leçons il pilote de moins en moins). Une fois les premiers atterrissages effectués on se concentre principalement là dessus en effectuant des tours de pistes: décollage, deux virages à 90°, remontée de la piste, puis nouveau virage en base, puis en finale, et atterrissage. En général on se contente d'un posé-décoller, pour multiplier les atterrissages et s'entraîner le plus possible.
Une fois que l'on sait décoller et atterrir dans les conditions optimales, on commence à s'entraîner (toujours avec instructeur à bord) pour les cas de panne: en particulier les pannes moteurs au décollage, mais aussi problèmes de volets etc., le tout en continuant les tours de piste et les atterrissages. À un moment l'instructeur considère l'élève prêt: il sort de l'avion et l'élève fait son premier vol solo: taxi, essais moteurs, décollage, un tour de piste et atterrissage.
De mon côté, j'ai appris le pilotage sur Aquila AT-01/A210, un petit deux places. Il est très léger (certaines versions sont considérées comme ULM), il pèse à peine 500 kg à vide, et le poids maximum est de 750 kg (avec carburant, passagers et bagages). Il ne va pas très vite (environ 100 nœuds ou 180 km/h), mais il est chouette à piloter. Comme il est très léger, il est très vite secoué par le vent, et dès que ça souffle un peu il est compliqué à poser car il veut continuer de planer (il a une finesse de 14). Au début j'ai réussi à pas mal voler (deux fois par semaine quand tout allait bien), donc la maniabilité s'est faite en environ 6 mois et 23 heures de vol. À ce moment là, mon instructeur est descendu de l'avion et j'ai fait mon premier vol solo. Tout s'est bien passé, sans grand stress, vue la préparation, et je n'ai même pas ressenti d'appréhension au final. Comme tout le monde dit, je pense que je m'en souviendrai toute ma vie, mais en pratique il ne s'est pas passé grand chose, hormis un petit sermon (gentil) du contrôleur sol lors du retour au parking après le vol: j'avais mal compris les instructions qu'il m'avait donné et je ne me suis pas arrêté comme indiqué (mais pas d'incursion de piste, tout va bien).



Après le premier solo, on continue les tours de pistes et du solo de temps en temps, et surtout on commence à faire des navigations: au lieu de rester à Lognes (LFPL) ou aux aérodromes alentours (LFPK à Coulommier, LFAI à Nangis), on peut commencer à préparer des vols un peu plus lointain, autour d'une demi-heure par exemple. Dans mon cas j'ai été à Moret-Episy (LFPU), à Troyes-Barberey (LFQB) et à Pontoise (LFPT). Pour préparer une navigation, il faut à la fois prévoir la route elle même (tracer la route sur la carte aérienne, préparer un « log de nav » avec les distances, les temps et les caps à disposition pendant le vol), mais aussi vérifier la météo, les informations règlementaires comme les NOTAM (Notice to Air Men), la quantité de carburant nécessaire etc. Pour moi, au début en tout cas, une préparation de vol me demandait entre une et deux fois le temps de vol effectif. La préparation initiale (navigation etc.) est complétée juste avant le vol par une dernière étude des conditions météo etc. Lors du briefing pré-vol (pendant la formation avec l'instructeur, puis au moment du test avec l'examinateur, et ensuite avec soi-même) on vérifie chaque domaine (navigation, météo, notam, carburant etc.) et à chaque fois on vérifie que tout est OK pour le vol. Dans l'aviation, beaucoup, beaucoup de choses tournent autour de la sécurité (ce qui se comprend, en cas de soucis il ne suffit pas simplement de lever le pied et se mettre sur le bas côté).


Une fois avoir pratiqué quelques navigations, on retourne vers les pannes, et en particulier quoi faire en cas de panne en campagne: panne moteur au milieu de nulle part, où il faut prévoir un atterrissage d'urgence, ou encore une panne radio. Là encore, une fois prêt (et, dans le cas de mon club, après avoir passé avec succès l'examen théorique), on commence les navigations solo (sur les 10h de vol solo nécessaire pour passer le test, il faut en avoir fait 5 en navigation). Dans mon cas, j'ai fait des navigation vers Troyes, puis Dijon-Darois (LFGI) et j'ai fait ma navigation trois-branches (nécessaire aussi pour passer le test) vers Chalons-Ecury (LFQK) et Pont-sur-Yonne (LFGO).
Juste après ça, quand je commençais à me sentir près pour le test, le confinement lié au COVID-19 a démarré, clouant au sol avions et pilotes pour plusieurs mois. Même après le déconfinement ça a été un peu compliqué de reprendre, et j'étais un peu rouillé et j'ai refais un peu d'entraînement. J'ai finalement passé le test au debut de l'été, mais le premier essai n'a pas été suffisant: j'étais vraiment très stressé, et honnêtement sans doute pas complètement prêt. Du coup j'ai fait un peu de réentraînement pendant l'été, et finalement, courant septembre, j'ai passé le test final, qui cette fois a été réussi.
Après un peu de paperasse (rendue un peu compliquée mais pas dramatiquement non plus par l'épidémie qui reprend un peu), ma licence de pilote privé est finalement arrivée au courier.
Et maintenant que je peux voler à peu près quand et comme je veux, l'automne est finalement là, avec un temps au mieux maussade. Du coup planifier des vols devient un peu compliqué. Pour l'instant, et même si techniquement je peux prendre des passagers avec moi, je refais quelques vols solos sur des terrains familiers. Avant de plus tard pouvoir emmener un passager avec moi en Aquila, et peut-être me faire lâcher sur un quatre places comme le DR400.



Corsac@18:31:29 (Echoes)
Saturday 04 January 2020 (1 post)
Après un peu d'interruption, nouvelle liste de films pour 2019.
Toujours une année pas très remplie, toujours pour les mêmes
raisons:
- Ben is back: 11 février 2019, UGC Ciné Cité Les Halles
- Le chant du loup: 25 mars 2019, MK2 Bibliothèque
- Avengers: Endgame: 28 mai 2019, MK2 Bibliothèque
- Yesterday: 13 juillet 2019, MK2 Quai de Seine
- Never grow old: 12 août 2019, UGC Montparnasse
- Once upon a time in Hollywood: 14 août 2019, UGC Ciné Cité
Bercy
- Anna: 15 août 2019, UGC Ciné Cité Les Halles
- Joker: 28 octobre 2019, MK2 Bibliothèque
- La reine des neiges 2: 7 décembre 2019, Grand Rex
Dans les mentions spéciales, j'ai beaucoup aimé Ben is
back et Yesterday. Un peu déçu par Once upon a
time in Hollywood mais pour être honnête c'est un pur
Tarantino, juste je me suis un peu lassé de la violence gratuite,
je crois.
Corsac@15:17:50 (Roadbook)
Saturday 21 December 2019 (1 post)
Aujourd'hui les jours rallongent \o/
Corsac@16:00:21 (Roadbook)